Pages in category 'BitTorrent' The following 6 pages are in this category, out of 6 total. Sep 03, 2020. Sep 01, 2020.
Whether you’re totally new to torrenting, or a seasoned pro looking to take your privacy to the next level, this guide is for you.
We know that digital privacy and new technology has a learning curve and can seem intimidating when you first dive in. This guide is intended to be a comprehensive introduction on how to stay safe an secure while downloading torrents online.
What you’ll learn: Everything from the basics of how torrent activity is monitored, how to protect your identity while downloading, and how to avoid malware, viruses and other security threats.
Topics:
- The Legality of torrents
- Torrent Monitoring
- Challenges
- IP Address
- Encryption
- Solutions
- VPN
- Proxy
- Nonsolutions
- Torrent Clients
- Viruses & Malware
- Realtime detection
- Antivirus
The Legality of BitTorrent
The torrent p2p protocol (bittorrent) is a fully legal file-sharing technology. It’s important to understand the distinction between the legality of the technology itself and how you choose to use it. Whether your own torrent downloads are legal vs. illegal depends entirely on what files you’re torrenting, who owns the rights (or if they’re public domain), and where you’re located. Different countries have different laws when it comes to filesharing/copyright issues.
To put it simply:
- Bittorrent itself is a legal technology. It is a decentralized protocol for transferring large files efficiently and quickly.
- If you share copy-protected files, you could be breaking the law depending on what country you live in and whether you were an uploader or just a leacher.
- Most penalties for downloading copy-protected files are civil (like a fine) rather than criminal, but local laws vary widely between countries.
How to find legal torrents:
There are dozens of sites online that index/host 100% legal torrent files. Most legal torrents are either files who’s copyright has expired (and are now public domain) or files that have been released with a license that permits free and open sharing/distribution.
Here are resources to find the best legal torrent sites:
While there are thousands of fully legal and public domain torrents available online, many bittorrent users also knowingly or accidentally download copy-protected. This may be completely legal (for personal use) in some countries or could be a violation of copyright law in others.
Because of the messy gray areas, uneven enforcement and unclear licensing of most public torrents, many bittorrent users take steps to prevent monitoring and protect their privacy while downloading.
How Torrents Are Monitored
BitTorrent’s greatest strength (distributed filesharing) is also it’s greatest privacy weakness. Torrent files can be downloaded in pieces from many (sometimes hundreds) of seeders at once. This lets you download large files like 4k videos incredibly fast. But it comes with an important tradeoff:
Torrent downloads are easy to monitor because all IP addresses sharing a file are public!
There are dozens of organizations that monitor torrent downloads from public trackers. These include:
- Researchers
- Internet Service Providers
- Law Enforcement Agencies
- Governmental Organizations
- Law Firms and Patent Trolls
- Data-mining firms and websites
Some sites like IKnowWhatYouDownload even make their data public. For example, here’s 1400+ IP addresses that have downloaded a certain adult torrent recently (and that’s just in the USA).
There 2 ways that your torrent history is tracked:
- Public IP-address: A numerical address that can expose your location and even exact identity. Every member of a torrent swarm can easily see your real IP address (if you don’t hide it).
- Direct Monitoring: Your Internet Service Provider and/or network administrator (at school for example) have direct access to your data stream. They can perform manual or automated packet inspection to see that you’re downloading torrents.
The Challenges of private torrenting
IP-address monitoring
This is the #1 way torrents are tracked, mostly because it’s so darn easy. Thanks to centralized torrent trackers as well as the DHT protocol, simple software can quickly connect to a swarm and log all the IP addresses.
And if you don’t take steps to hide your real IP address, then this could be you:
How to prevent IP address monitoring: It’s not that hard. Yes, peers must be able to see an IP address when you connect, but it doesn’t have to be your real one. You can use a non-logging VPN or proxy to route your torrent traffic through an IP address that can’t be traced to you. So peers only see the VPN server, not your real location & identity.
Direct Monitoring by your Internet Provider
Have you ever received a warning letter from your internet provider for downloading a specific torrent? They may have been notified by a 3rd-party based on your IP address (as discussed above). It’s also possible they directly monitor your traffic and noticed torrent activity.
In fact, many ISP’s worldwide choose to monitor, throttle or completely block torrent activity using sophisticated firewalls and automated deep packet inspection to spy on your internet usage.
They can also hijack your DNS lookups and browser searches to see if you’re visiting torrent sites.
How to prevent packet inspection: Use a Virtual Private Network (VPN). It will wrap your internet traffic in a layer of unbreakable encryption so even your ISP can’t see what you’re doing online.
The Tools: The best methods for secure torrents
Here you’ll find all of the most common tools you can use to keep your torrent activity private and secure from monitoring agencies and even your internet provider. They’re ranked from best-to-worst
Virtual Private Network (VPN):Best Option
VPNs are the most commonly used privacy tool in the torrent community. The reasoning is simple: VPNs are easy to use, cheap, and very effective.
Most important rule: Always use a torrent-friendly VPN that doesn’t keep logs.
How it works:
When you connect to a VPN server (using simple software) it will do 3 things:
- Route all your internet traffic through their server
- Assign you a new public IP address (that is nearly impossible to trace to you)
- Encrypt all your traffic so your Internet Provider can’t read it
Which VPN to use?
We’ve tested dozens of VPNs. Here are 5 great options (all of them keep no logfiles whatsoever).
How to set it up
All these VPNs come with their own easy-to-use software. Simply sign up, download and install the software, and connect to a server in a torrent-friendly country. For extra security, turn on the kill-switch to prevent IP leaks.
We’ve also got complete setup guides for popular torrent clients including:
SOCKS Proxy
The closest alternative is a proxy service. It’s kind of like VPN-lite. You configure the proxy inside your torrent client and it hides your IP address from peers just like a VPN. One key difference is that most torrent proxy services don’t have encryption. Instead, you can use the built-in protocol encryption in your torrent client.
One nice thing about using a proxy is once you set it up it just works. There’s no need to turn it on or load software every time you want to start a torrent.
Which Proxy Service to use?
There are two very important factors when choosing a proxy service:
- It MUST be SOCKS (not HTTP) or it won’t hide your IP address from peers
- It should be a logless proxy service
Don’t worry, torrent-friendly SOCKS proxy providers are easy to find. In fact, several of our favorite VPN services actually include SOCKS proxy access in every subscription.
These are the best VPNs with a SOCKS5 proxy:
How to set it up:
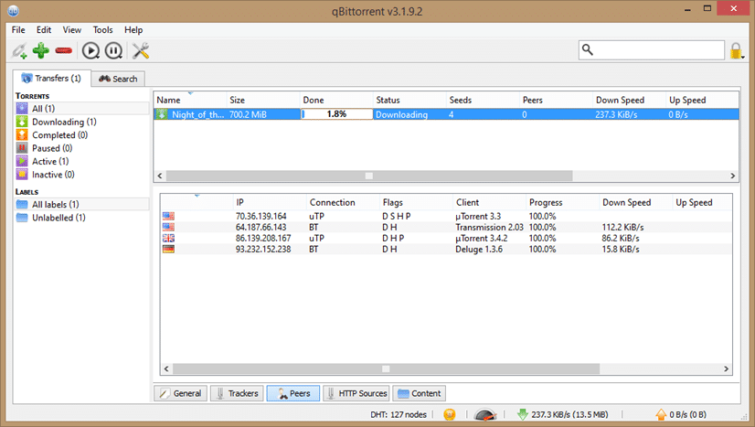
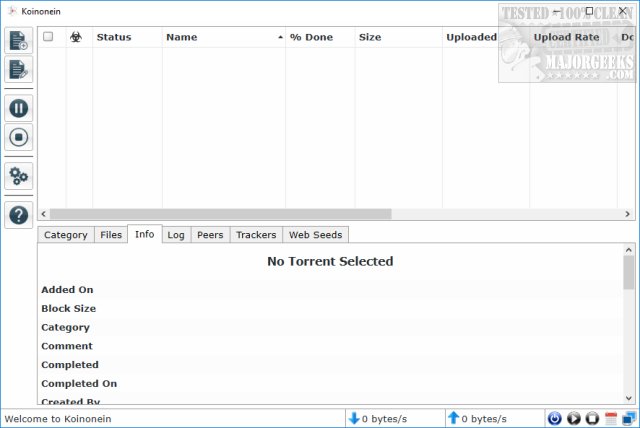
When you subscribe to proxy service, they’ll provide you with your login credentials (username/password) as well as the port number and proxy address. That’s all you need to setup your torrent client. Proxies are most secure when used with: uTorrent, Vuze, Deluge or QBittorrent.
You can add RC4 encryption to your proxy using your torrent client’s p2p encryption settings. This isn’t as secure as a VPN but may be good enough to circumvent firewalls and throttling.
Seedbox: if price is no object
If you are a high-volume torrenter and need to meet seeding quotas, you might consider a seedbox.
Seedboxes are basically a torrent client installed on a remote VPS that runs 24/7. You control it from a web interface and it downloads/seeds your files from the server. You can then transfer the files to your computer via https.
Seedboxes are paid services and quite expensive (typically 3-5x the cost of a VPN).
Seedbox Pros:
- Files download really fast
- You get a lot of upstream bandwidth
- You can seed files without taking up space on your home computer
Seedbox Cons:
- Expensive. $20+/month is typical
- Have to transfer files twice (to seedbox then to your computer)
- Less secure than VPN and many services are shady
- Most Seedboxes only allow private trackers
The Worst Tools: ineffective or dangerous
There are several less-effective tools that people sometimes try to use.
Best case, they’re slow or cumbersome. Worst-case, they’re completely useless or even dangerous. These are the tools you should avoid:

Blocklists (Peerblock/PeerGuardian/iBlocklist)
Blocklists are basically spreadsheets of large numbers of ip addresses. The idea is that if you can block the ‘bad’ torrent peers, you can only connect to safe ones. This sounds nice in theory but in reality most blocklists don’t actual block the peers you need to worry about (like torrent trolls) and instead just reduce speeds and number of connections.
Blocklists also don’t hide your IP address from trackers (which bad actors can scrape). Finally, they don’t have any encryption whatsoever.
Don’t bother with them. Seriously. They’re useless.
More detail: The truth about Peerblock
Non-SOCKS Proxies
There are stories all over Reddit and other forums from people who grabbed some free HTTP proxy credentials off a website and soon after received a warning letter from their ISP.
You should never ever use any sort of HTTP or HTTPS proxy for torrent privacy. They simply do not work.
Why: HTTP proxies can only transport HTTP data (like the content of a website). They are incompatible with p2p protocols like BitTorrent. If you try to use an HTTP proxy for peer communications, your torrent client will just ignore the proxy, exposing your true IP address to peers and offering no protection whatsoever.
Most Secure Bittorrent Client Download
Always. Use. SOCKS. Proxies.
i2p
i2P is an anonymity network that routes traffic through a cluster of remote servers, mixing your traffic with other traffic. In theory it’s a good idea and it actually does work.
The problem is that it’s extremely slow. You can expect speeds around 50kbps (not suitable for downloading video or other large files).
If you want to check it out, the easiest way is the i2p plugin for Vuze.
Malware, Phishing & Viruses
Beyond the legal & privacy risks, downloading torrents from public trackers can have other security risks as well. These include the threat of malware & phishing ads as well as viruses and trojans (embedded in files).
Fortunately if you’re aware of the threats and take common-sense steps to combat them, you can mitigate much of the risks.
Browser Threats: Malware, Phishing & Malicious Ads
Most blackhat torrent sites (those that host primarily pirated content) are tough to monetize by traditional means. They can’t run google or Amazon ads to generate revenue, so they’re forced to deal with some sketchy clients to make money.
Most Secure Torrent Client
Unfortunately this puts you at risk.
Commons malicious ad types you may run into:
- Cryptocurrency miners (browser malware)
- Phishing sites (pose as a legit site and steal login credentials)
- Virus Sites (get you to download malware or viruses disguised as legit files).
- Ads with javascript or flash-based exploits to hack outdated browsers
Frankly it’s exhausting dealing with the garbage ads on these sites, and nobody actually wants to click them because we all know they’re trash sites.
Here’s how to deal with them: Mac what to buy.
- Keep your browser updated. Make sure you have auto-updates enabled for your preferred browser. Don’t delay updates. Most people don’t realize that browser (and other software) updates frequently fix security flaws and bugs rather than just adding new features.
- Disable flash. it’s an outdated technology and has huge security flaws. Just disable it altogether, or at least make sure flash scripts don’t run without a prompt.
- Use a separate browser for torrent sites. You can use different browser software just for torrenting, and keep the settings pretty locked down. For example, disable all cookies, flash & javascript.
- Use an Adblocker. You can’t click ads if you can’t see them. Use Ad-block or another ad blocking software to remove or minimize ads. Some VPNs such as Cyberghost even have ad-blocking built in.
- Use real-time virus protection. You need an antivirus that can detect viruses and malicious scripts in realtime (before they infect your computer). Invest in a premium antivirus like Avast Pro or Mcafee. Windows Defender is a free option that’s bundled with windows 10 and now offers realtime virus protection. And don’t be that idiot that tries to pirate antivirus software (it’s obviously loaded with viruses).
Trojans & Viruses in torrent files
Torrent sites and ads aren’t the only threat. Hackers frequently upload malicious software and trojans to torrent sites. It’s usually embedded in torrents with executable installation files such as video games or software.
To avoid trojans completely, you’d be smart to just avoid any torrent with an executable file (stick with media files like video).
If that’s too restrictive for you, make sure you have a good (paid) antivirus, and scan every torrent file before you install it. Seriously, there’s some frightening spyware out there, frequently bundled with games on torrent sites.
Another option is to just run your torrented files through virustotal, a free online virus scanner that checks files against dozens of antivirus scans.
Summary & additional resources
Download crossover. As we’ve learned, it’s possible to dramatically improve the security and privacy of your torrents with a few simple tools. By taking a multi-layered approach, you can add additional redundancy and better privacy.
For example, you could use a VPN and Proxy together so that if one fails, the other should still work to keep your real IP address hidden from torrent spies.
The best tools:
- VPN
- SOCKS5 Proxy
- Seedbox
Most Secure Bittorrent Client Free
The Worst Tools:
- HTTP Proxies
- i2P
- Thoughts & prayers
And no matter which privacy method you choose, you should try to add some level of encryption for your torrents.
Here are some step-by-step setup guides:
And once you’ve set everything up, you’ll need to test it to make sure everything is working.
Here’s how to check your torrent IP address and verify the VPN is working.
Most Secure Bittorrent Client Login
Do you have any comments, questions or tips we missed? Let us know below!
Bittorrent Client
Ryan McCarthy
Most Secure Bittorrent Client Software
Ryan is the editor and head reviewer. He's been a tech geek and digital privacy enthusiast since the Y2k freakout in '99. When not writing BitTorrent tutorials, he can usually be found sipping a lager or playing pickup football (the real kind).